Microarchitectural Integrity Sign-Off
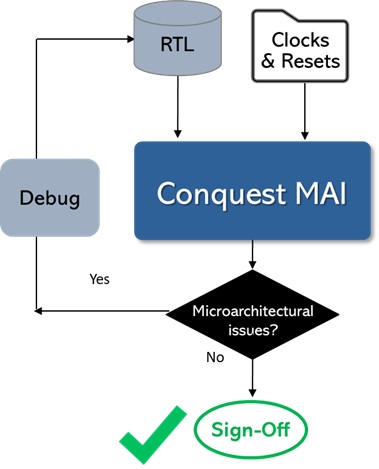
Conquest MAI is the industry’s first microarchitectural integrity sign-off tool. Its quick setup and extremely fast performance enable designers to include it during RTL sign-off.
Conquest MAI automatically infers and identifies standard functional components (SFCs), even when they are distributed across the design hierarchy.
It then performs localized, automatic checks early in the design flow to verify microarchitectural integrity. These checks go beyond the scope of RTL linting, exceed practical formal verification capacity limits, and are difficult to target effectively using simulation.
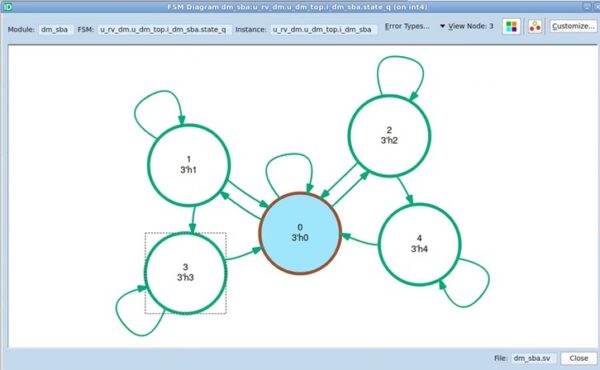
Conquest MAI’s advanced debug capabilities enable visualization of the inferred functional intent of each SFC, supporting deep design understanding and exploration. For example, it generates FSM diagrams and SFC functional block schematics.
Key Takeaways: Conquest MAI microarchitectural integrity sign-off
Minimally Boolean: Enabling MAI sign-off during RTL sign-off
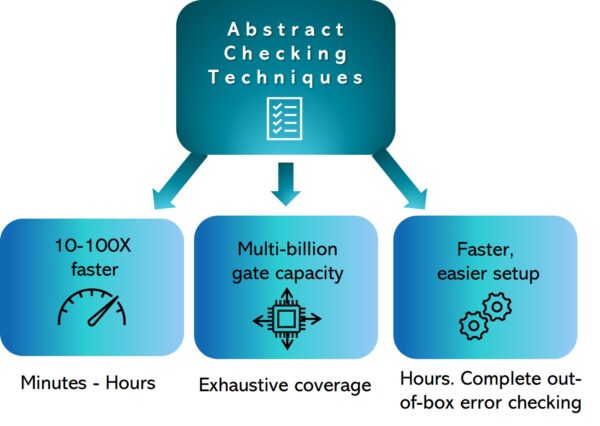
Because simulation and formal verification methodologies rely heavily on Boolean analysis, they each have limitations. Formal is slow with significant capacity limits for exhaustive analysis, while simulation requires large resource investments.
Conquest MAI is only minimally dependent on Boolean methods. It primarily uses abstract checking methods rather than full Boolean state-space solving — applying custom solutions for specific problems. This approach:
- Runs 10X–100X faster than formal, analyzing a million gates in minutes.
- Exhaustively covers billions of gates in hours without black boxing.
- Requires only hours for setup with out-of-the-box checks – no testbenches or assertions required.
This combination makes it practical for designers to start microarchitectural integrity checking during early RTL design — well before beginning simulation.
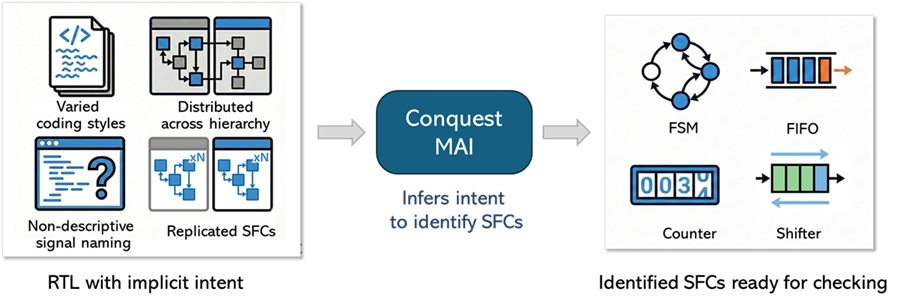
Inferring Functional Intent to Identify SFCs
Conquest MAI infers functional intent directly from RTL by identifying Standard Functional Components (SFCs) such as FSMs, multi-port RAMs, FIFOs, stacks, counters, and shifters. This process looks past RTL syntax to understand functional behavior, enabling SFC identification even when structure and intent are obscured by coding style, hierarchy, or distribution across modules.
Conquest MAI’s intent inference is:
- Agnostic to coding style: Identifies components whether they are implemented using case statements, if-else logic, or conditional operators.
- Cross-hierarchy: Infers components even when their logic is functionally split across multiple modules.
- Semantic rather than syntactic: Does not rely on variable naming conventions (such as current_state/next_state); instead, it analyzes logic flow to recognize constructs even when they use obscure descriptors, as well as complex arrays and generate statements for multiple identical SFCs.
Simulation and formal verification tools operate on explicitly written logic and Boolean behavior; they do not infer functional intent. Conquest MAI understands both the design’s implementation and its functional intent, establishing the foundation for microarchitectural integrity sign-off.
Leverages existing Meridian CDC or Meridian RDC setup
Conquest MAI requires minimal setup to ensure accuracy of analysis. The clocks and resets must be identified, as well as the mode configuration settings necessary for functional operation. Conquest MAI is able to use existing environment files from Meridian CDC and/or Meridian RDC. The tool can also automatically create an environment file template for review.
Microarchitectural integrity checks
Conquest MAI’s understanding of the functional components and its microarchitectural analysis technology enable it to run microarchitectural integrity checks on the SFCs that are not practical with other verification methods.
- Simulation can show data corruption or data loss when the appropriate sequence of conditions are applied, but debug is tedious and lengthy
- Formal typically has capacity issues and generally requires additional constraints for accuracy.
- RTL linters cannot infer SFCs beyond basic FSMs
Below are a few examples of unique microarchitectural integrity checks that Conquest MAI can perform.
FIFO Read / Write Reset Mismatch
Check: Verify that the read/write counters and their associated status signals (empty/full) use the same reset signal. A mismatch in reset sources between a pointer and its associated status flag will leave the FIFO in an inconsistent state, likely causing data corruption.
Out-of-range counter usage
Check: Verify that counters are being compared against values that are within the inferred operational counter range. Comparing counter values with values outside of the counter range can signal an error in coding, either in the specified counter range or the usage.
FIFO Overflow / Underflow
Check: Verify that FIFO control logic enforces valid access based on FIFO state: writes are blocked when the FIFO is full, and reads are blocked when the FIFO is empty. Overflow causes data loss by overwriting unread entries; underflow causes invalid or repeated data to be returned.
Visualizing Inferred SFCs for Debug
Conquest MAI applies the same inferred intent analysis when identifying SFCs to generate visualizations that present the inferred structure and behavior of each SFC, independent of RTL coding style.
These graphical representations accelerate debug by making it easier to understand why a condition exists and how the observed behavior emerges from the design. Examples include:
- Schematics show the implementation, including any module hierarchy
- SFC functional block schematics that show SFC interfaces, and control relationships
- FSM diagrams that show states, transitions, resets, and state conditions such as self-loops, unreachable paths, or illegal encodings, enabling rapid verification of state reachability and control flow
By visualizing inferred SFCs, Conquest MAI enables faster root-cause debug of detected issues, with clear validation of inferred intent versus designer intent. The result is confident exploration of complex or unfamiliar microarchitectural behavior.
Additionally, Conquest MAI contains an SFC viewer that provides a global view of the designs SFCs, along with details of each SFC.
What is Microarchitectural Integrity Sign-Off?
Microarchitectural Integrity Sign-Off is a static verification methodology that verifies the functional correctness of standard functional components (SFCs) within RTL designs. The methodology involves identifying SFCs, even when they are distributed across the design hierarchy, and subsequently checks to ensure their implementation and usage adheres to expected functional behavior and design intent.
Key Takeaways: Conquest MAI microarchitectural integrity sign-off
This section summarizes how Conquest MAI, the industry’s first microarchitectural integrity sign-off tool, automatically infers and verifies FSMs, FIFOs, counters, stacks, and shifters using minimally Boolean analysis — catching a class of functional bugs that simulation cannot efficiently target and formal cannot practically scale to.
- Product. Conquest MAI is the industry’s first microarchitectural integrity sign-off tool, using static analysis to automatically infer and verify the functional correctness of standard functional components (SFCs) — FSMs, FIFOs, counters, stacks, and shifters — early in the RTL design cycle.
- Key Challenge. SFC issues such as FIFO overflow/underflow, counter out-of-range usage, FSM encoding errors, and reset mismatches are a class of bugs that simulation cannot efficiently target and formal cannot practically scale to; Conquest MAI closes this gap.
- Competitive Advantages. Conquest MAI technology uniquely identifies SFCs across different coding styles—then uses minimally Boolean analysis to quickly verify microarchitectural integrity, enabling exhaustive microarchitectural static checks that were previously impossible.
- Design Flow Fit. Conquest MAI can be deployed after RTL linting and before CDC/RDC, simulation, and formal verification — catching microarchitectural integrity issues at the earliest practical stage of the design flow.
- Engineering Benefits. Engineering teams accelerate their verification schedules by achieving out-of-the-box checks within hours of setup, and graphical SFC visualizations — FSM diagrams, functional block schematics, and an SFC viewer — accelerate root-cause debug by making inferred design intent immediately visible.
- Ecosystem. Conquest MAI fits into standard RTL design flows to provide deep microarchitectural sign-off with minimal overhead; it can leverage existing Meridian CDC or RDC environment files to accelerate setup time.